Cybersecurity Risk from Employees: How to Assess and Reduce It
Employees represent the single largest source of cybersecurity risk in most organisations — not because they are careless, but because they are targeted. Attackers invest significant effort in social engineering, credential theft, and manipulation specifically because the human layer is harder to patch than software.
This guide approaches employee cyber risk as a management problem, not a training problem. It covers how to measure your exposure, which employee segments carry the most risk, the organisational controls that reduce incidents, and how IT and HR need to work together to make those controls stick.
If you're looking to understand the root causes of why employees make mistakes — the cognitive and behavioural factors behind errors — that's covered in our companion post: Human Error in Cybersecurity: Causes, Examples, and Prevention. This guide focuses on risk assessment and control.
How to Assess Your Organisation's Employee Cyber Risk Exposure
Before putting controls in place, you need to understand where risk actually concentrates. Not all employees carry equal risk — access level, role, and behaviour patterns create distinct risk profiles.
High-risk employee segments to assess:
- Privileged users (IT admins, finance staff, executives) — high-value targets with broader access
- New employees — unfamiliar with processes, higher susceptibility to social engineering
- Remote workers — reduced visibility for IT, greater reliance on personal devices and home networks
- Repeat phishing clickers — employees who have failed two or more simulations represent a measurable, ongoing risk requiring targeted intervention
Metrics to track for risk quantification:
- Phishing simulation click rate by department and seniority
- Credential reuse incidents detected via dark web monitoring
- Incident report volume and source (who reports, how quickly)
- Policy violations logged by DLP or CASB tools
How the Modern Workplace Expands Your Employee Risk Surface
Cybersecurity risk continues to rise as organisations become more digital and interconnected.
Several factors are contributing to this growth:
Remote and hybrid work environments
Increased reliance on cloud applications
Employees accessing systems from multiple devices
More complex supply chains and third-party access
AI-generated phishing and impersonation attacks
Each new system, login, or application increases opportunity — not only for productivity, but also for exploitation.
Because human behaviour is the primary attack surface, the question for security managers isn't whether employees will be targeted — it's which employees carry the most risk.
For a full breakdown of the types of mistakes employees make and why, see Human Error in Cybersecurity
Human Error vs Insider Threats
Employee-related cybersecurity risk generally falls into two categories.
Human Error
Human error includes unintentional actions such as:
Falling for phishing emails
Misconfiguring cloud permissions
Mishandling sensitive data
These incidents are accidental and account for the majority of security breaches.
Insider Threats
Insider threats may involve:
Disgruntled employees
Negligent security practices
Compromised employee credentials
While insider threats receive significant attention, most organisations face far greater risk from unintentional behaviour than deliberate misuse.
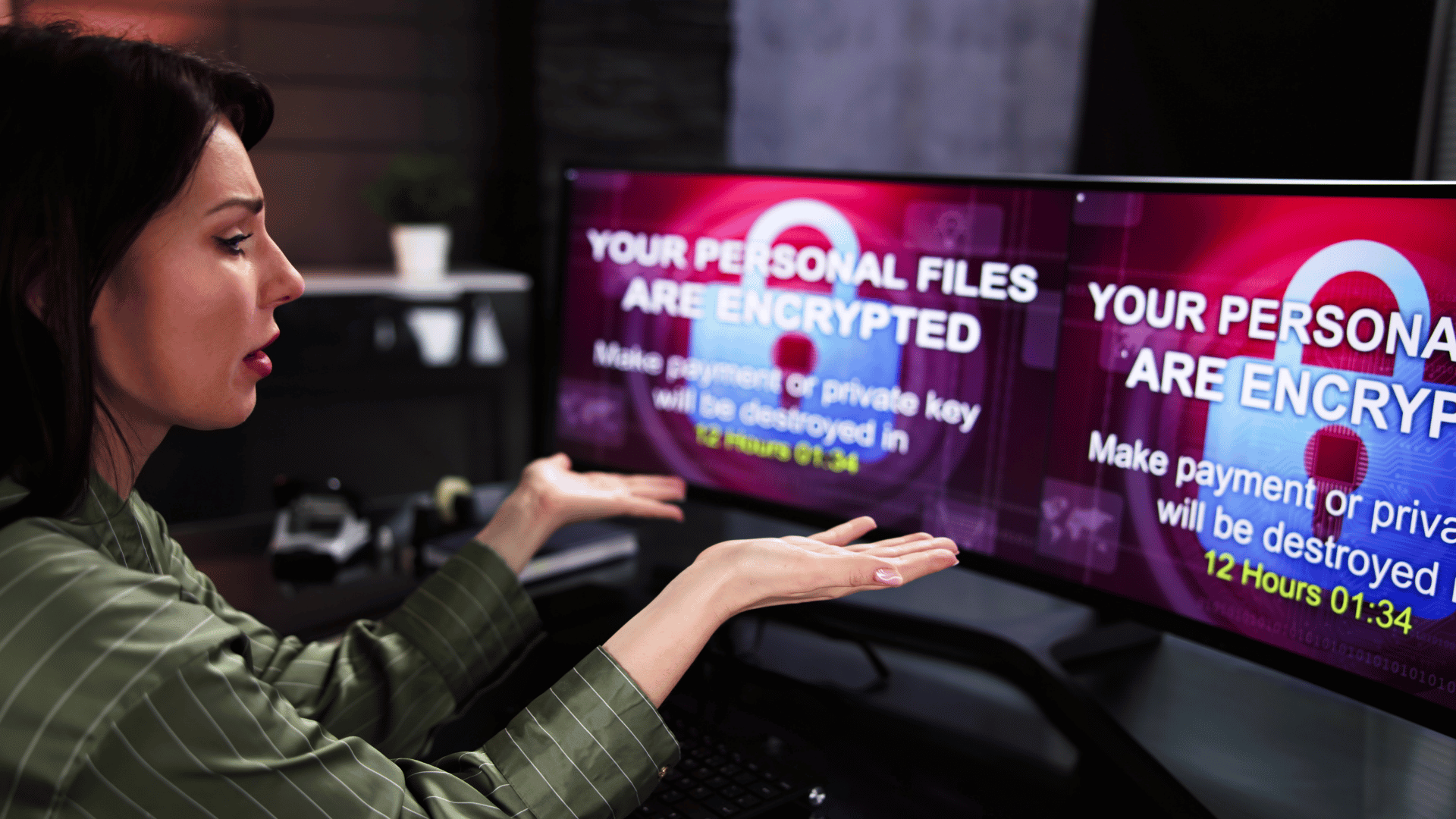
Real-World Examples of Employee-Driven Cyber Incidents
Employee-based cybersecurity risk often appears in familiar scenarios:
Business Email Compromise (BEC): An employee receives a fake executive email requesting an urgent payment.
Credential Harvesting: A staff member logs into what appears to be Microsoft or Google, unknowingly giving attackers access.
Invoice Fraud: Finance teams receive altered supplier banking details.
Accidental Data Exposure: Files are mistakenly shared publicly through cloud platforms.
Compromised Admin Accounts: One stolen password grants broad system access.
In each case, technology was present — but human trust was exploited.
Why Technology Alone Can’t Eliminate Cybersecurity Risk
Security tools play a critical role, but they cannot eliminate risk entirely.
Firewalls, endpoint protection, email filtering, and Zero Trust frameworks reduce exposure — but they cannot prevent every human decision.
Attackers continuously adapt their techniques to bypass automated detection. When a threat looks legitimate, security tools may allow it through, leaving the final decision to the employee.
In modern cybersecurity:
Technology reduces risk — employee behaviour determines outcomes.
How to Reduce Cybersecurity Risk Caused by Employees
Reducing human-related cybersecurity risk requires more than annual compliance training.
Effective strategies include:
Continuous security awareness training rather than one-off sessions
Phishing simulations that reflect real-world attack techniques
Role-based education tailored to job responsibilities
Clear incident reporting processes with no blame culture
Regular reinforcement through short, ongoing awareness content
Behaviour-based metrics to track improvement over time
The goal is not perfection — it is preparedness.
Building a Human-Centric Cybersecurity Strategy
A strong cybersecurity posture combines technology with culture.
Organisations that reduce risk effectively:
Treat employees as part of the security solution
Encourage early reporting of suspicious activity
Reinforce learning regularly
Involve leadership in awareness efforts
Measure behaviour, not just completion rates
When employees understand why threats exist and how attacks work, security becomes proactive rather than reactive.
Cybersecurity Risk Isn’t a Technology Problem — It’s a Human One
Employees are not the weakest link in cybersecurity.
Unprepared employees are.
As cyber threats become more sophisticated, managing cybersecurity risk requires recognising that people sit at the centre of every system. Technology provides protection, but awareness, behaviour, and culture determine resilience.
Organisations that invest in both security tools and employee education are far better positioned to reduce breaches, minimise disruption, and protect their business long-term.
Frequently Asked Questions about Cybersecurity Risks
-
Because urgency and fear reduce critical thinking. When people feel pressured, the brain prioritises speed over accuracy, making them more likely to click links or follow instructions without verification.
-
Yes. Training improves awareness, but fatigue, multitasking, stress, and heavy workloads can override learned behaviours. Phishing attacks are designed to exploit momentary lapses, not lack of knowledge.
-
Phishing targets human behaviour instead of software vulnerabilities. Attackers manipulate emotions and cognitive biases, which is why technical security tools alone cannot fully stop phishing attacks.
-
Today’s phishing emails often use legitimate branding, realistic language, lookalike domains, and personalised information. Some attacks are so well crafted that they appear identical to real business communications.
-
When employees understand why phishing works — not just what it looks like — they are more likely to pause, question urgency, and recognise manipulation before taking action.